How to Secure Your Office Wi-Fi Network

Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall app.
Wi-Fi is ubiquitous today in workplaces large and small. However, in case of small and medium-sized businesses, too often their Wi-Fi networks turn out unsecured and vulnerable. An unsecured Wi-Fi network can present an ideal pathway for hackers and malefactors to disrupt your operations or steal your company data. What’s more, businesses of these sizes don’t generally have the resources or dedicated IT personnel in-house to properly secure the network and monitor it in real-time.
There are many steps that outside IT consultants or internal specialists can take to help secure an office Wi-Fi network. Here, we present just a few of these steps, the ones that will provide the biggest bang for your buck (and time).
Try VPN Unlimited for FREE and massively enhance your WiFi network security
Use WPA2 Enterprise Security
The security used in your network should be at least WPA2 (rather than WEP or other, older and more hackable protocols). One of the best ways to secure your network and prevent legacy issues with departed employees or lost or stolen devices is by using WPA2 in Enterprise mode. Rather than a single network login, WPA2 Enterprise sets up individual logins for each employee. They each get their own encryption key, too, meaning they can only access their own chunk of corporate traffic. So, even if a key is compromised, it doesn’t provide access to the rest of the network.
Utilizing WPA2 Enterprise security requires setting up a RADIUS server, using a cloud-based one, or enabling this function on your existing server. It basically holds the database of user IDs and passwords. Once that’s set up, you can convert your access points to WPA2 Enterprise mode, with the RADIUS server IP, port, and access credentials. Then, everyone on your network logs in with their user ID and password – and if one is compromised, you just delete that entry from the database.
This can be further refined to prevent other forms of attack by utilizing client-server certificates with the RADIUS server. When properly configured, the user’s machine will first confirm if the server is legitimate and not a spoof (client-side server verification) before communicating any login credentials to it. This functionality is available within the 802.1X standards – you simply select the requirement, input the server address, and select the certificate-issuing body – then you can lock out any changes, so no new servers or certificate authorities can be added into the mix.
Use a VPN Service

Once all your internal security and traffic is sorted out, one of the best additions you can make to secure your network is a VPN service. Too often, bad actors seek out targets on the Internet at large, or through a corporate website, and then use social engineering to find a weak link and try to crack accounts. Without using a VPN, most company networks have static outbound IP addresses that are relatively easy to log and trackback.
With a VPN, no matter where your employees go online, the true IP address or addresses of your network access points will be obscured. So, even if an employee clicks on a bogus link or visits a compromised site, the data gathered won’t let anyone know the true IP address and the source of the traffic. In a lot of ways, using a VPN this can be compared to having a blocked number on a caller ID. You can call out and go where you want to go without the risk of divulging corporate or personal information.
There are lots of other advantages to having a VPN for your employees as well. Traffic is encrypted with essentially unbreakable encryption, meaning no one – a competitor, a government, or even your ISP – can snoop on your traffic. Further, a VPN service is portable – meaning if your employees are traveling or working remotely, they can still be secure, and on your network. It also may be essential for employees traveling in countries with highly restricted Internet policies, e.g. China, so they can keep access to all the services they need.
Physical Security
One of the most commonly overlooked aspects of network security is physical protection. Ensure that the network’s hardware is as secure as possible, such as by having the main router, switches, and whatnot in a locked room or cabinet. Placing access points mounted to the ceilings can also help, as this is ideal for the best signal, and makes it explicitly obvious if anyone unauthorized is climbing up a ladder to fiddle with them.
Network Name and Router Logins
While it should go without saying, one thing to check is to ensure that administrator accounts for routers and other access points in the network are customized, and NOT using the defaults, or you’re just asking to be hacked. The network name should be modified as well.
Defaults that broadcast the name or model of the router as the SSID make it too easy for hackers to breach – don’t do them such a favor. Likewise, it may not always be a good idea to advertise your business name via the SSID – something more generic or memorable enough for your employees, but without giving away who the network belongs to, is often the best bet.
Scan for Unauthorized Access Points
Periodically, you should scan the network for unauthorized access points. Whether added by an employee with a bad reception at their end of the building, or by someone covertly with ill intent, they can present easy targets to get into your network. Most routers, switches, and other hardware come with built-in network access point scanning capabilities. If there are pro-active measures available, such as alerting or requiring authorization to add an access point, so much the better.
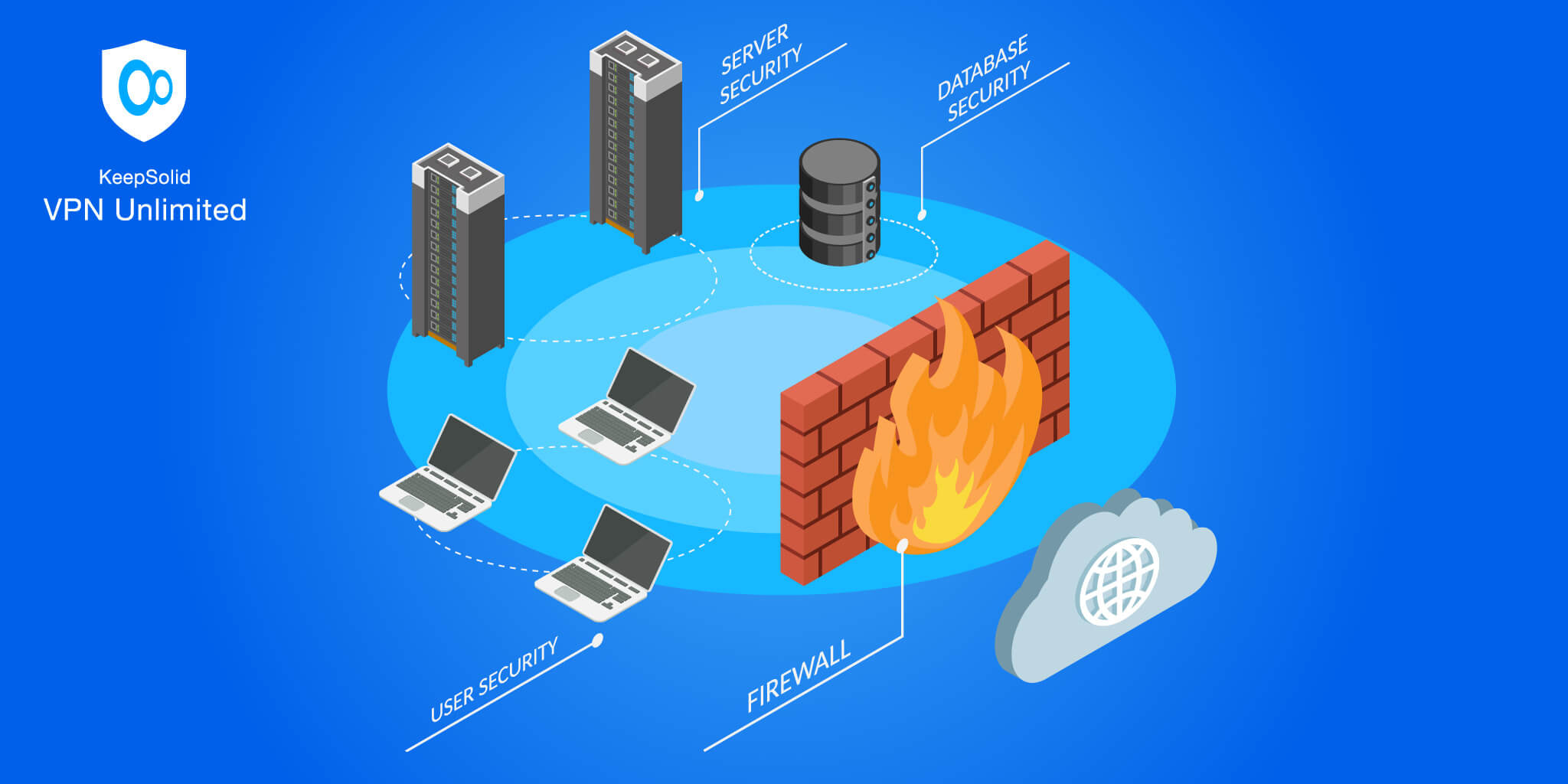
Firewalls
Conclusion
In summary, there are many steps that even the smallest or least tech-experienced business can take to improve the security of their Wi-Fi network. Whether it’s tightening physical security, changing logins for routers and access points, or more advanced techniques like using WPA2 Enterprise protection or checking for rogue access points, you can always improve your security, often without much effort or cost. For maximum security, once you have your internal network secured, you’ll want to provide employees with a VPN service for their external traffic, adding yet another layer of protection.
This is a contributed article.