Security World Cup 2018 Results, And What to Make of Them

Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall app.
About mid-June, we at KeepSolid have launched a cyber security quiz, coincided with the 2018 FIFA World Cup. We aimed to see how tech savvy the general audience is, and to help users identify the blanks in their knowledge of the topic. If you haven’t taken this quiz yet and would like to check your proficiency with the concept of internet security, we highly encourage you to do this BEFORE you go on with this article, as there will be some spoilers ahead. Ye be warned!
Security World Cup scores and what they mean for your internet protection
Since its launch, over 2000 players participated in our Security World Cup 2018. We have amassed a body of data based on their answers and noticed a sort of a pattern there. Namely, certain questions proved to be notably tricky for the majority of users. Today, we’d like to delve into these specific issues, make them more comprehensible, and give you a general hint or two about cyber security.
But first, let’s see how our players identified themselves. 2018 Security World Cup standings were as follows:
- 36% of participants chose to play as an Everyman character
- 26% chose the Traveler
- 24% tried their hands at being Hackers
- only 14% felt like picking the Online Buyer
Now, let’s take a look at some of the most critical online security fallacies of our users!
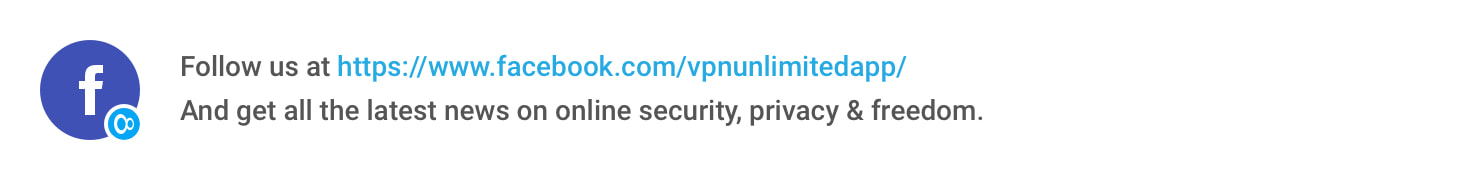
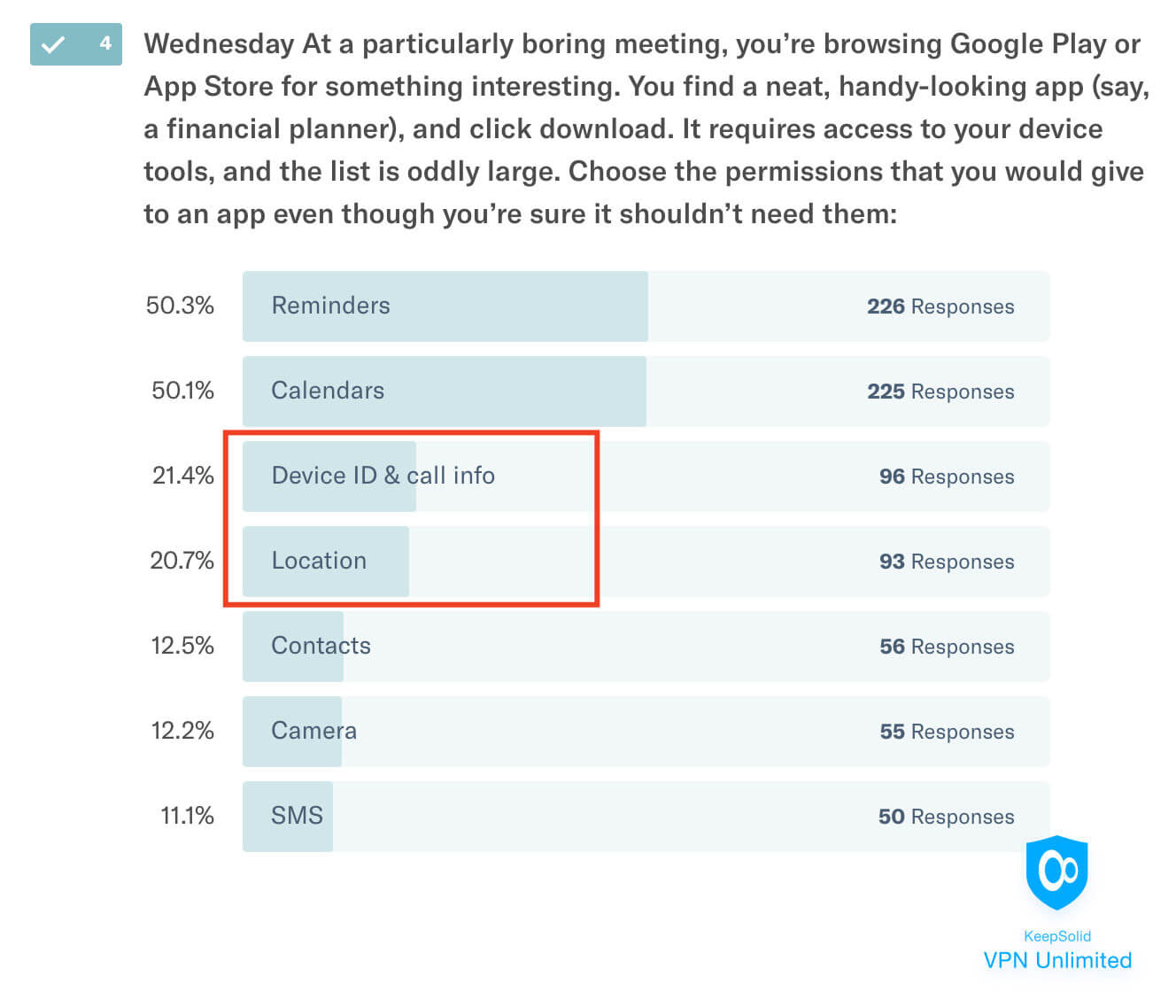
1. Justified permission requests
A number of questions on our cyber security test asked users to judge the adequacy of various apps’ permission requests. It’s no secret that this is one of the easiest ways for a malicious application to compromise your device and get access to your sensitive and personal data. Well, imagine our surprise when the statistics showed that many participants felt completely content giving away permissions to apps that clearly shouldn’t have requested them!
Above you can see an example of such mistake. Device ID, call info, and especially location information can provide infinite opportunities to a hacker. Yet, we are so accustomed to sharing this data with any first comers that we no longer feel cautious about this.
The same applies to the example below. You know, access to the camera is not required for editing per se. But it’s such a common request in all sorts of apps that it doesn’t set off any alarms for most of us anymore.
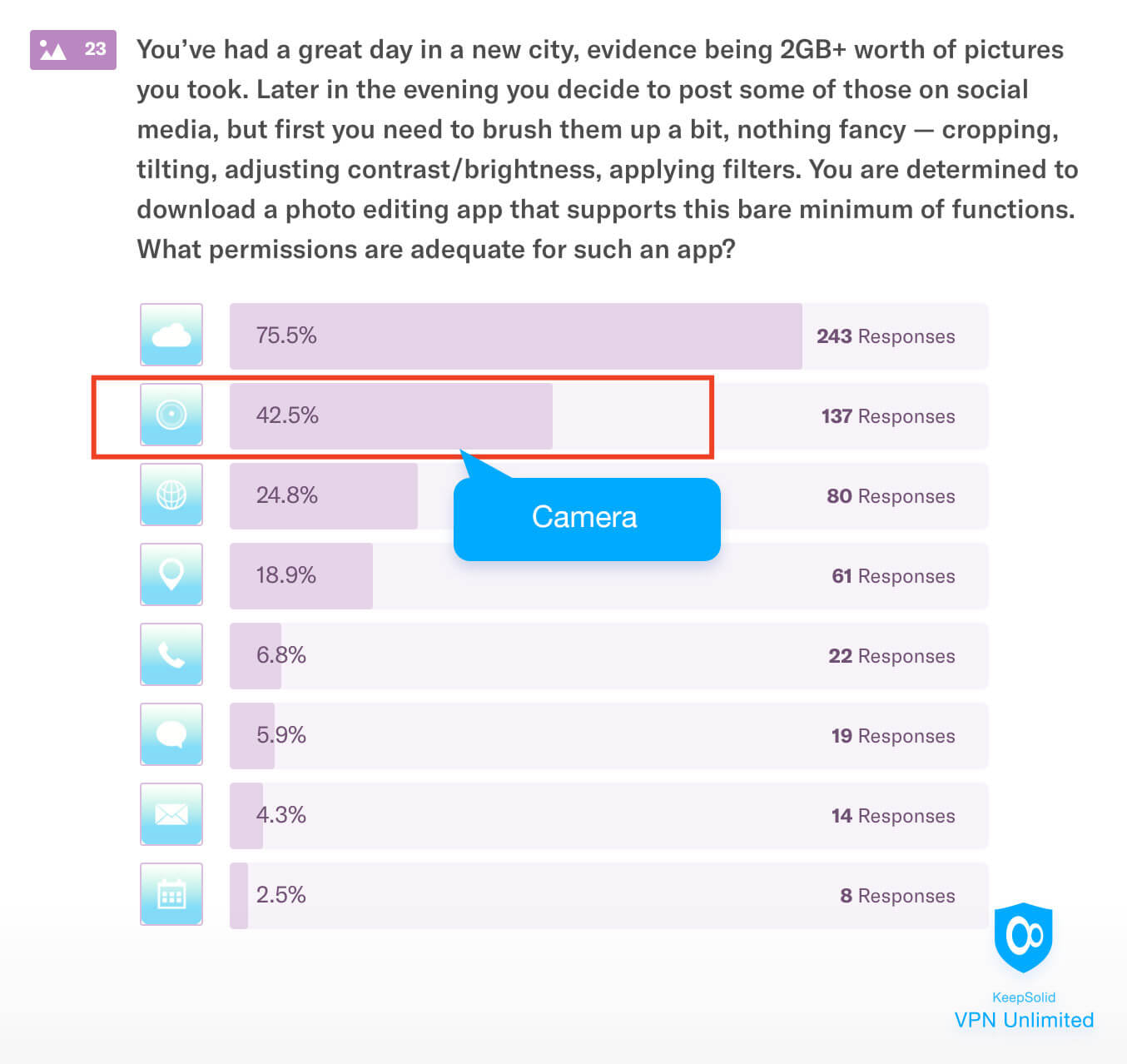
2. Dangerous links
Another popular misconception can be illustrated with the following picture. As you can see, almost half of the players felt like a different country’s domain is enough of a reason for concern. In reality, this alone is nothing to worry about, as long as the website utilizes https encryption and its address doesn’t include weird characters combinations.
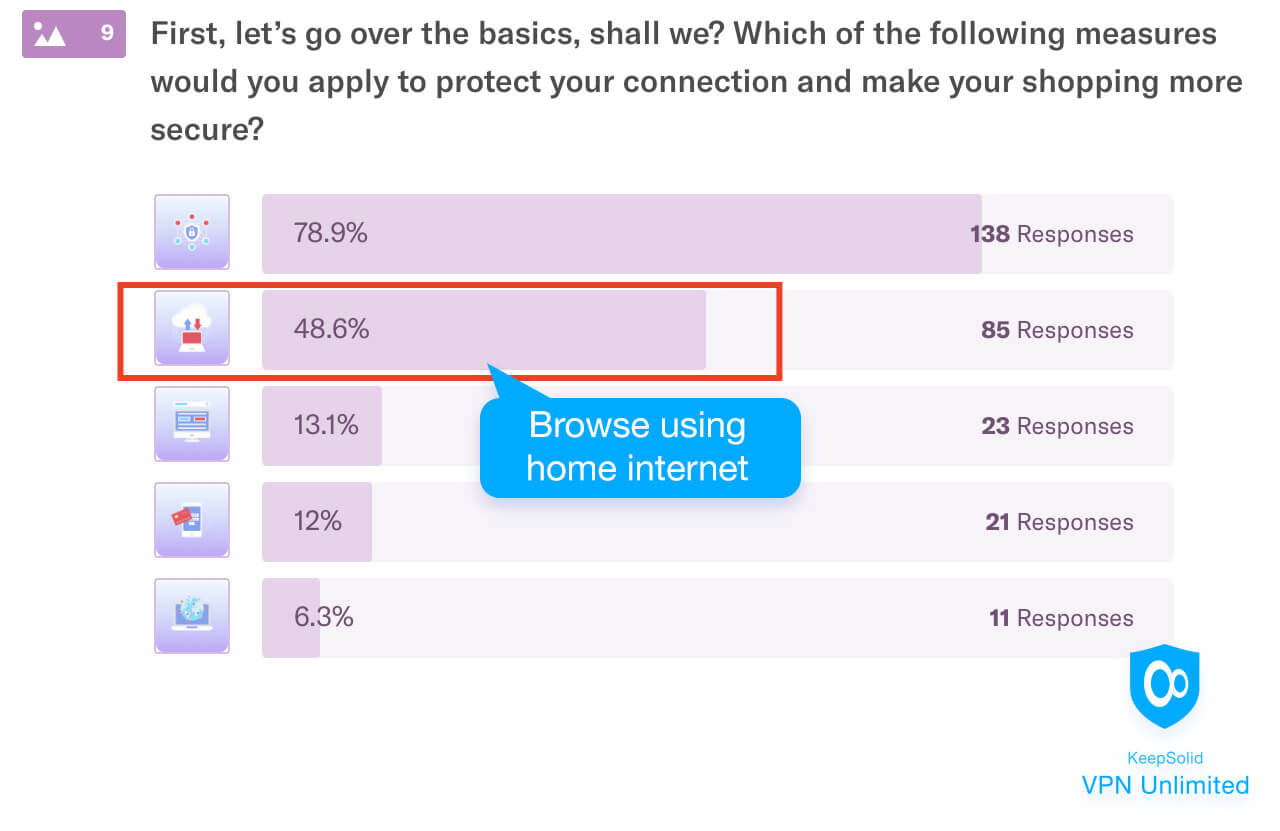
3. As safe as a house (network)?
People tend to perceive their homes as their castles. No surprise that almost 50% of respondents in our WC 2018 named their home internet a completely secure place, as seen below. Alas, in reality a common home WiFi network is not the least bit better protected than a public one. So, unless you employ proper security measures, feeling safe at home is but a self-deception.
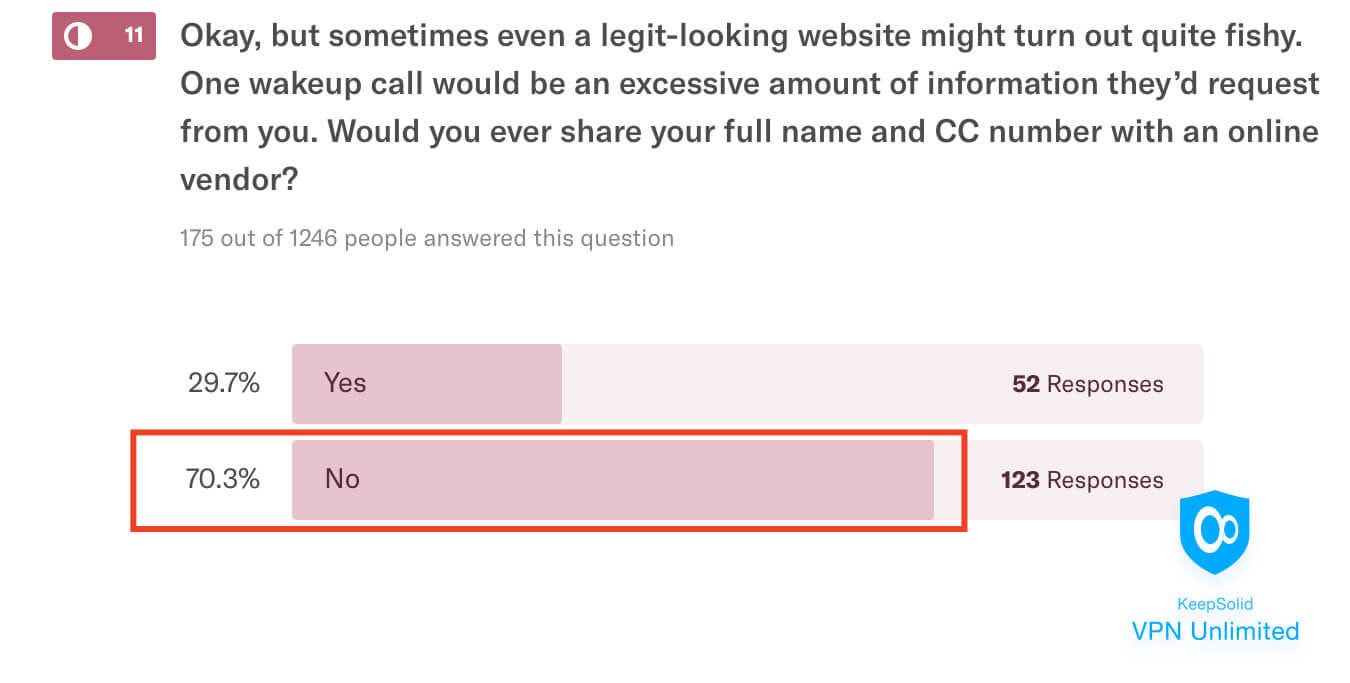
4. Information giveaway
Ironically, some of the misconceptions stem from overreacting, rather than inadvertence. For one, 70% of users claimed they wouldn’t share their full name and СС number with a vendor. But this is actually quite a normal and necessary practice. How else would vendors know who to send the purchase, and charge its cost?
5. Social engineering and PGP
For the finale, let’s take a look at two minor yet amusing mistakes from the Security World Cup 2018. The first one regards the concept of social engineering. All of a sudden, about 45% of our players appear to believe that this idea refers to using social network accounts to collect data about their owners. Sure, we can see where such point might be coming from. But the social engineering is, of course, about psychologically manipulating people into divulging sensitive information.
The second funny misconception was about the PGP abbreviation expansion. Almost 40% of respondents thought it meant “Protection Guarantee Protocol”, probably because of how formally this sounds. Well, what do you know! Turns out a much less-formal sounding “Pretty Good Privacy” is actually correct 😀
Be smart about online security
It’s never too late to acknowledge the white spots in your education and get to fixing them. Socrates’ “I know that I know nothing” is as relevant as ever, and we hope that this piece helped you fill the gaps in your knowledge of cyber threats and security. If you’d like to learn more on this topic, subscribe to our blog about internet security and privacy!