Top 5 Notorious Hacking Attack Types and How to Avoid Them

Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall app.
Nowadays, we can hardly imagine even a single day without modern technologies and gadgets, such as smartphones, computers, tablets, smart watches, etc. They are penetrating every sphere of our life to make it easier and more colorful. This mainstream helps us to immerse into the web surfing, exchange selfies with friends, or do business even being far away from the office. But not everything is so perfect in the online space.
There are a shocking variety of attacks, which are rapidly spreading via the network and can harm your devices, as well as your sensitive data. More likely, now you have two questions in your head, “What types of attacks are the most dangerous?” and “How to protect private data against these threats?” We are ready to give you a comprehensive answer about this to help you recognize hackers’ tricks.
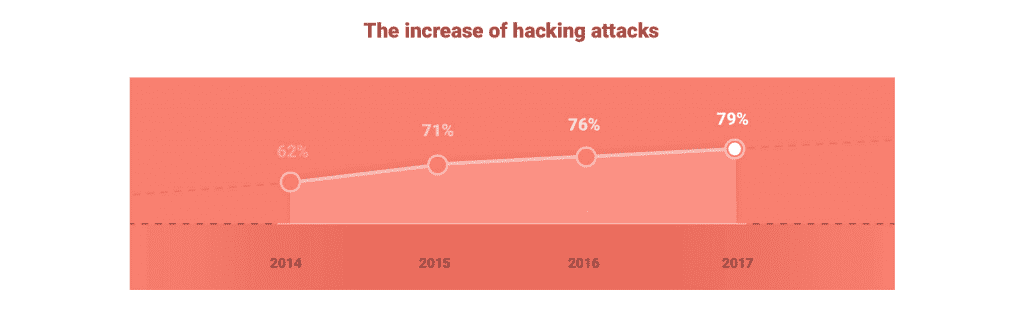
Today’s variety of malware and ways that hackers use to harm our online security is quite impressive. The amount of users who have become a victim of different attacks keeps increasing with no end in sight. The diagram below shows you how dramatically the situation has changed over the past 3 years.
This is why we decided to explore the issue and share with you the results. Check out this general overview of the attacks widely used by hackers and methods to prevent them.
- Malware
If your device begins to run very slowly, settings change by themselves and you can’t restore them, or the web browser contains the components you didn’t download, it’s a sure sign that the gadget is infected with malware. You’ve probably clicked on a pop up window or a link with malicious software when downloading some files or just surfing a non-trusted website. Now, cyber criminals can wreak all sorts of havoc on your device. The worst thing is that they are able to monitor your online activities, take control of your private information, and share or sell the data to unauthorized third parties. For this hackers use different shapes and sizes of malware, such as spyware, ransomware, viruses, worms, trojans, and scareware.
How can you prevent it? Avoid clicking and loading files from unknown sources and always keep your security software up-to-date.
- Malvertising
This new method was developed by adversaries to compromise your device with malicious software through online advertising. There are two possible ways when malvertising infection may happen.
First one is when you press on malicious advertisements, which are usually placed on high-traffic and trusted websites, for instance, BBC.com, Spotify, or The New York Times. These ads are often presented as pop-ups or alert warnings. Suspecting nothing, you install malware yourself just by clicking on them.
The second scenario doesn’t require your actions, except one. In this case, once you visit a website where malicious ads are, infected files automatically begin downloading to your device. You won’t even understand it is happening.
How can you prevent it? Install the anti-exploit technology to keep ads from loading onto your device and resist clicking on them.
- Phishing
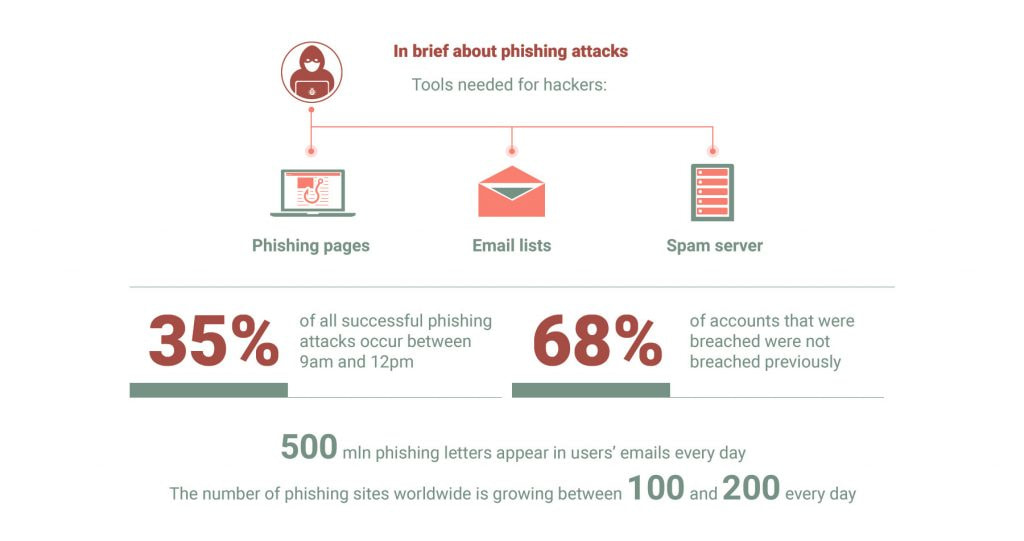
A phishing attack often masks as a request for sensitive data from someone you trust, like your friends, relatives, or colleagues. It looks like a legitimate letter with a goal to persuade users to share their personal data, such as real location, credit card details, password, etc. Recently, these emails have become much more complicated, making it much more difficult for users to distinguish a legitimate letter from a fake one. You can frequently see them in the spam folder. But be aware, they are more dangerous than advertising. Taking into account a huge amount of phishing attacks sent every day, even a small percentage of users who will take this bait is enough for scammers to reach their goal.
How can you prevent it? Check all the e-letters you receive and never share your sensitive information via the email.
- Password attacks
The name speaks for itself. This is the case when hackers try to access your profile by hacking the password. Generally, this threat doesn’t require any malicious code to be run on the devices. The cyber criminals try to crack encrypted data by means of a software which is installed on their system. The main point is while using a special dictionary of letters and numbers to make all possible combinations that can reproduce a password, hackers will get access to your profile sooner or later.
How can you minimize the chance of a successful attack? Create a strong password using a combination of letters, numbers, or symbols and change it periodically.
- DDoS attacks
Distributed Denial of Service (DDoS) attack is a kind of malicious try to bring down network services, websites, or servers on your device by the flood of the incoming traffic. Hundreds of thousands junk messages, such as connection requests or malformed packets, force the target system to slow down or even crash. As a result, this process prevents some or all legitimate requests from being fulfilled.
According to Wikipedia, DDoS attack is analogous to a group of people crowding the entry door or gate to a shop or business, and not letting legitimate parties enter into the shop or business, disrupting normal operations.
How can you prevent it? Regularly update your software and track your data flow to determine unusual increase in traffic.
How can you sneak away from hackers’ hands?
Despite the fact this article highlights only 5 possible hacking attack types you should know that there are hundreds of other online dangers which you may face. Always keep in mind that cyber criminals are very persistent and they leave no stone unturned in their efforts to create new online threats and find holes in our defenses.
Yet, our developers have done their best to keep ahead of them and designed the first-class solution, VPN Unlimited, with its top-notch security features. The app offers you a strong protection by using the most popular VPN protocols, such as OpenVPN® and IKEv2. Also within the pack you’ll get access to KeepSolid Wise technology – an elaborated service that will grant you boundless access and enhanced reliability.
But there’s more – now it’s possible to use your User Office to create custom VPN connections. This way you can manually build a connection and tailor it to best suit your needs. With VPN Unlimited, you get a higher layer of online security and privacy that enables you to enjoy safe and smooth online experience.
Download VPN Unlimited right away because it will protect your browsing and prevent snoopers from reaching your sensitive data.
“OpenVPN” is a registered trademark of OpenVPN Inc.