How to Make Sure Your Connection Isn’t Leaking: WebRTC, DNS, IPv6 Leaks

Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall app.
When we want online anonymity and protection, we resort to VPNs, but most of them make your connection only somewhat secure, sometimes leaking critical data and giving you away. Is your connection really protected? Read on to learn how to check that and patch if necessary.
There are several ways your connection can be leaking and revealing your identity even when using a VPN. Below we’ll cover the key ones.
With VPN Unlimited none of your private information is leaked
What is DNS leak and how to do DNS leak check
The Dynamic Name System (DNS) is a system that translates domain names into IP addresses. The translation requests are usually processed on ISP’s DNS servers, but if you use a VPN, DNS requests are routed to respective VPN provider’s servers.
For most operational systems, there are no risks of any DNS leaks ever occurring, but a technique employed in newer Windows systems, although designed to improve network performance, makes VPN users prone to exposing their identities. This is because Windows sends DNS requests in parallel, using all available channels, including those outside the VPN tunnel, and chooses the fastest.
A good VPN service for Windows should have a build-in DNS leak prevention mechanism. Want to check if your system leaks DNS? Click the below button to go to the DNS leak test page:
Run the DNS Leak detection test, wait till it is 100% complete and check the results. If your ISP’s location is not listed, it means your connection doesn’t leak your DNS requests.
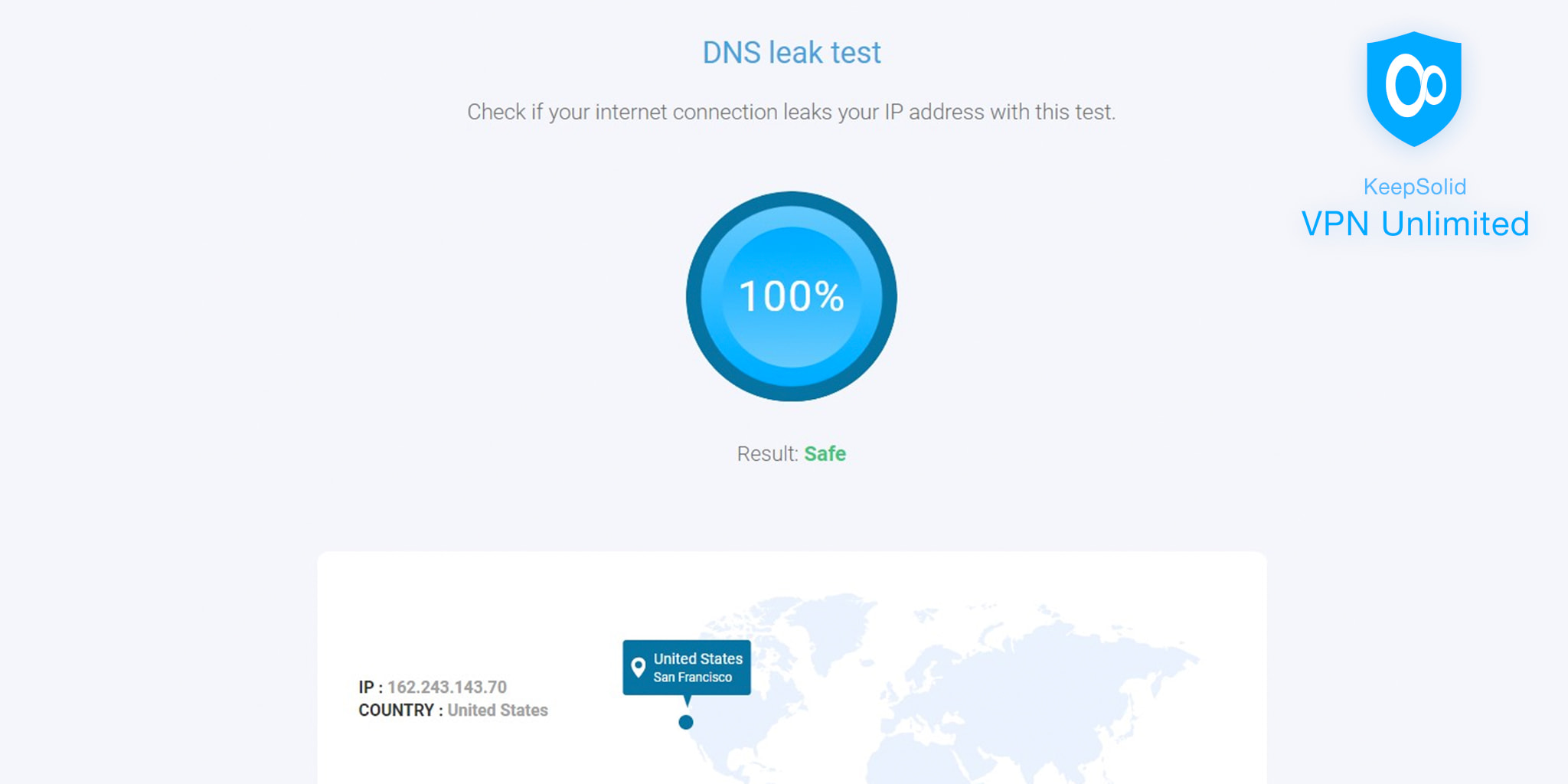
Generally, a DNS leak exposes your ISP’s IP address, not yours, but that can easily be traced back to you, and it can also be used by interested parties to collect your browsing history.
What is WebRTC leak and how to avoid it
WebRTC stands for “Web Real-Time Communication” and is an open-source project that provides browsers with APIs that allow direct P2P communication inside a web-page, eliminating the need for installing additional plugins or programs. A useful tool, no doubt, as it is called to improve browser-to-browser communication, but there is a shortcoming. And it’s of no small importance.
WebRTC can be implemented with just a few lines of JavaScript code, its requests are not listed in network console, and using it does not require a user’s consent. WebRTC is enabled by default in such browsers as Chrome, Firefox, and Opera. What’s so dangerous about WebRTC is that it leads to your true IP address leak even if a VPN is used.
VPN Unlimited browser extension has a built-in protection against WebRTC leaks
Blocking WebRTC leaks
The good news is that WebRTC can be easily disabled. There are 2 ways to prevent WebRTC leaks:
- Use VPN Unlimited browser extension with a built-in WebRTC Leak Prevent feature. Enable it and make sure you get the most possible anonymity and privacy online.
- Disable WebRTC in browser settings. Some, like Chrome, require a third-party plugin, and some, like Firefox and Opera, have a respective toggle in a privacy settings menu.
Check if there is a WebRTC Leak
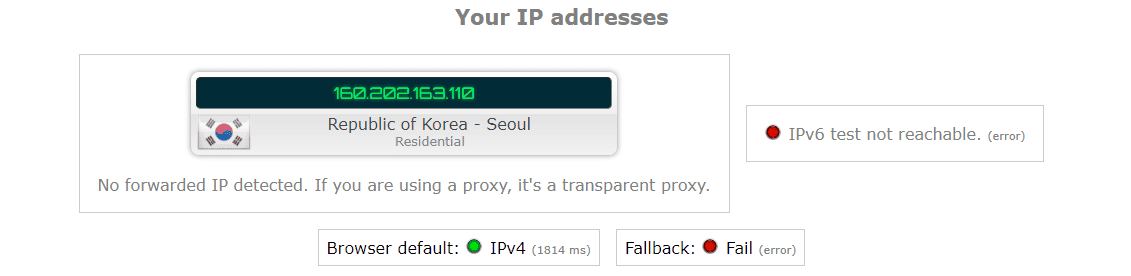
You can check if your connection exhibits WebRTC leak at https://ipleak.net. After you disable WebRTC support, there should be no server listed in the section shown in the picture.
What is IPv6 leak and how to fix it
IPv6 is the newer version of Internet Protocol called to mitigate IPv4 exhaustion problem. Since IPv6 is a future-proof standard, its present use is scarce, and sites that use it almost always allow IPv4 connections too. Leaks are possible if your ISP uses IPv6. To check if your connection leaks your IPv6 address, you can use the aforementioned https://ipleak.net. Check the IPv6 field. If it doesn’t show any numbers, then your connection is not leaking.
What is IPv6 leak protection
Generally, you can disable IPv6 connectivity altogether without any noticeable change in your internet experience. To do it, check out this guide for Windows.
Bottom line
The DNS, WebRTC and IPv6 leaks are not to be taken light-heartedly. Although not universal, they are rather dangerous. Each of them, with reasonably small determination, can put at threat your online privacy and reveal your identity. So, make sure to take all the necessary measures to stay protected!
