Time to Ask Yourself, “How Secure is My Password?”

Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall app.
Passwords are responsible for protecting our digital information. In many cases, they are the first and only line of defense. As our lives continue to move online, that protection becomes more and more important. If a hacker manages to get your passwords, this can cause all kinds of troubles. They could gain access to your bank accounts and siphon funds. They could block your computer or phone and ransom back the access. They could steal sensitive data from you or even your employer if you conduct work at home.
How hackers get your passwords
It’s important to understand how hackers typically end up getting your password. Here are some of the most popular tactics they use.
- Phishing: This is when a hacker or group of hackers creates a web page that replicates a site that you, and others, frequent. Common targets are bank login screens or other sites where people need to make payments. Should a user mistake this fake page for the real one, they will enter their username and password into the fields. Consider it a write-off then!
- Bait and Switch: This method is when hackers create an ad or other malicious link to try and bait users into clicking. Once the link is clicked, it automatically downloads malware onto your computer. This malware can do a lot of terrible things, the most common being a program that can “watch” you entering passwords and record them.
- Key Logging: Like the bait and switch, keylogging starts with a user getting tricked into downloading a malicious piece of software. The keylogger then literally tracks every keystroke you make. The hacker can then start combing through the data looking for compromising information like usernames and passwords.
- Fake WAPs: We all love free WiFi. There’s nothing like getting comfortable in your local coffee shop and getting online through their wireless access points. However, hackers will set up fake WiFi’s that mimic the local WAPs. If you should join these by accident, the hackers can view all the data streamed between your device and their remote server. Don’t forget to use reliable VPN services, like VPN Unlimited, to prevent such mishaps!
No single platform is more secure than others password-wise
The key thing to understand is that you are the one responsible for protecting your passwords. Software developers and email hosting services will do what they can to keep hostile forces from infiltrating their own servers, but they can’t stop a customer from individually falling victim to a hacking scheme.
No such programs or platforms protect you more than others, nor do they put your safety their top priority. To protect your passwords the responsibility is on you to take the necessary precautions in order to stay safe. Remember, it’s much easier for a hacker to steal from a user directly than it is to hack Google or Microsoft.
Password strength best practices
Users are not without their own techniques or “weapons” against these malicious attacks. Here are some things to keep in mind when setting and protecting passwords
- Never use personal information in your passwords
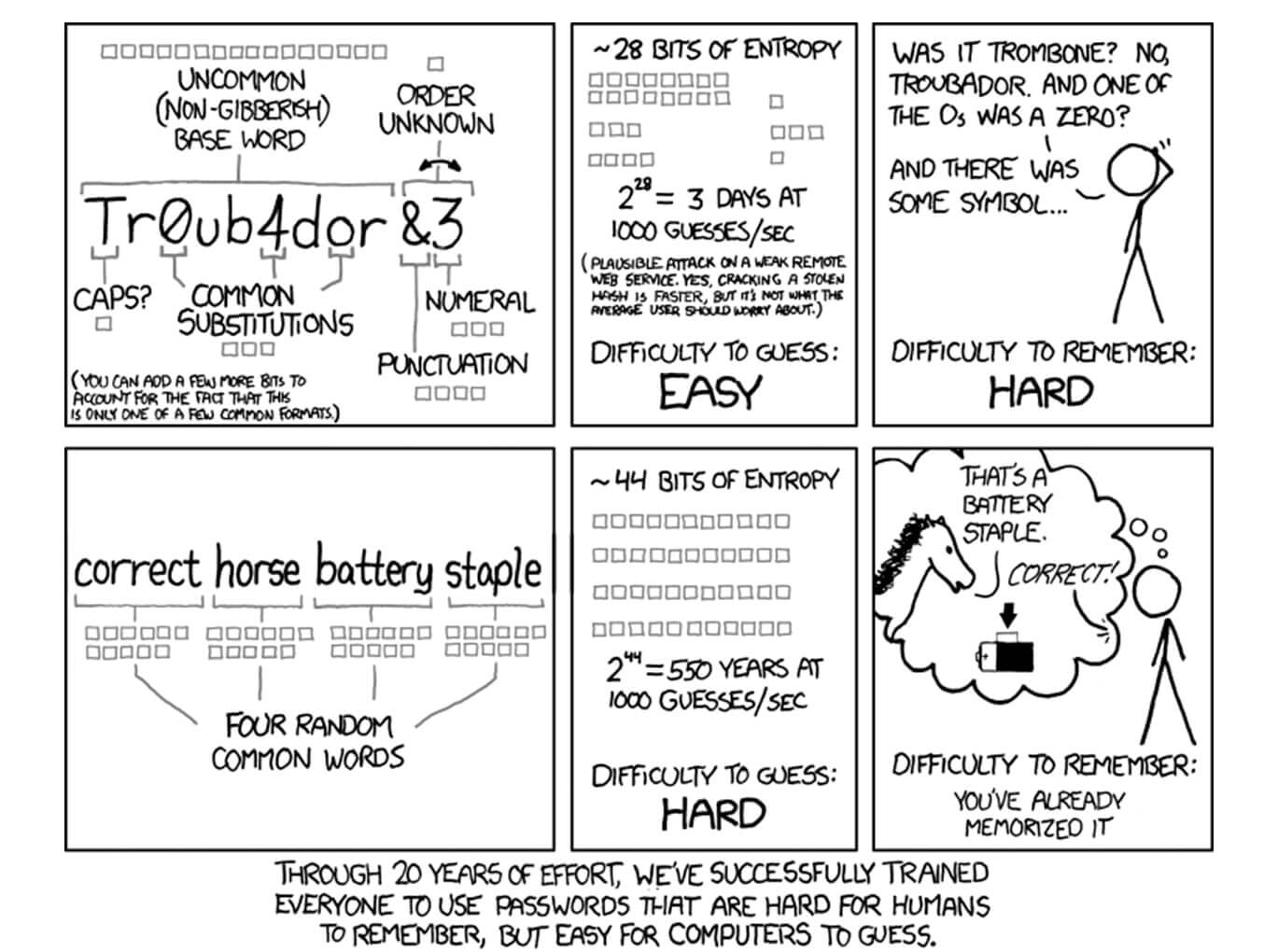
- The longer the password the better
- Make your passwords a combination of letters and numbers including capitals, regardless if a site requires it or not
- If you can’t remember them, use long, complex phrases meaningful for you
- Change your passwords regularly
- Use password managing software to keep track of multiple good passwords, do not use the same password for everything
- Try out random password generators, they can get lots of hassle off your chest
- Use the Gibson Research password tester found here to test your password strength
Pay attention to the links you click and the servers you connect to when using the internet. Change your passwords often and make sure they are complex. Stay safe out there, and you will be ok. And once you’ve learned the ropes of reliable password generation, don’t forget to use VPN Unlimited to protect your personal data from non-password related threats!
This is a contributed article.